In the new world of Web 3.0, users are taking more control as the technology stack becomes more resilient, decentralized and secure. Many of the world’s leaders and leading tech companies, such as the EU, Google, and Apple, are taking steps to support this new future. For companies trying to find new customers, this may feel like a step backward to the old days of “spray and pray,” where marketing and advertising dollars were unable to tie back to a key performance indicator (KPI). We are here to tell you there are still many effective ways to optimize your dollars and find the customers you want to have discovering, purchasing and reviewing your products.
Table of contents
1st vs. 3rd-Party Data
This is data collected on a customer through linking of Personal Identifiable Information (PII), such as email, phone number, first & last name and hashing of credit card used. This data is then collated based on this individual and used in numerous marketing campaigns & strategies.
| 1st-Party Data | 3rd-Party Data |
|---|---|
| First-party data consists of data that the business has directly collected based on the user’s activity, analysis, transactions, and volunteered information from internal sources. This data is kept inside the business, and competitors do not have access to it. | Third-party data consists of data that the business has received, usually as the result of correlation between PII, against that of an external source. Others on the network have access to similar or connected details even if they are in competition with each other. |
| Examples Include:Birth Day/Month in ProfileBilling/Shipping Address in a Profile or on TransactionsFirst/Last Name in a Profile or on TransactionsEmail Address through Sign-Up, Log-In or TransactionsPurchase History (Frequency, Quantity, Items)Locations of Purchase (Store, Online, Apps)Survey InformationCustomer Service Messages Sentiment or Key TopicsModeling from this data | Examples Include:Profile linking of groups, friends, pages, topics (Facebook)Personal details, birthday, college and graduation, work history, family tree, relationship/marital status (Facebook)Likes, Follows, Hashtags (Instagram)Connection to others (Facebook)Board interest mapping (Pinterest)Ad interactions (Google/Bing)Genre Correlations (Spotify)Comment, Chat & Review Sentiment through Emoji, Ratings, Keywords (Disqus, Yotpo, Bazaarvoice)Other Analytics Data (On 3rd-Party Network) |
| This can be used for segmentation of emails or campaigns that are built on external networks to find similar customers. Example:If you buy primarily sale, we will send the customer sale emailsIf the customer spends “x” dollars a year, get VIP status on website and in-storesIf the customer only shops in-store for shirts, and most customers that shop in-store and online buy pants online, advertise pants to the customer in an emailAfter purchasing a product the customer receives an email asking to leave a review, giving the business “social proof” of the product | This is primarily used for modeling. i.e. creating known buckets of intent, interests and propensities. Example: If you subscribe to “Fitness Magazine” or are in a “Weekend Workout Group,” you would be in an interest group for “fitness”If you have a meditation app, it could be assumed you have a high propensity for “yoga”If you have a college degree, you could be in a higher income bracketIf you are born in “x” year, you are in the 18-24 age group |
Consent Management for Cookies & Tracking
Several nations and businesses have expressed concern about the collection and use of customer data. Consent has been demanded by consumers regarding the use and collection of such data to protect their privacy. Nations have enacted laws in response to this demand, and many businesses have enacted legal requirements. Those with a higher moral and ethical fiber have further expanded this practice.
In many of these laws, such as GDPR (General Data Protection Regulation – EU) and the CCPA (California Consumer Privacy Act – USA), consent is required for the collection, use, and sale of personal information.
This does not just apply to cookies, but also applies to tracking information on third-party tools like Google Analytics, selling of email capture lists, or even serving relevant ads in affiliate programs. Tools such as OneTrust provide cookie consent and other consent compliance practices, like data request management. Companies have included the ability to enforce these rights in their tools.is vein, vein, Google has cookie consent to enforce Google Tag Manager code, and Apple that surfaces per-app Opt-In for any App or In-App-Ad that is tracking data on your interactions.
(read other article on “how does a cookie work” – see below)
Traditional 3rd-Party Audiences
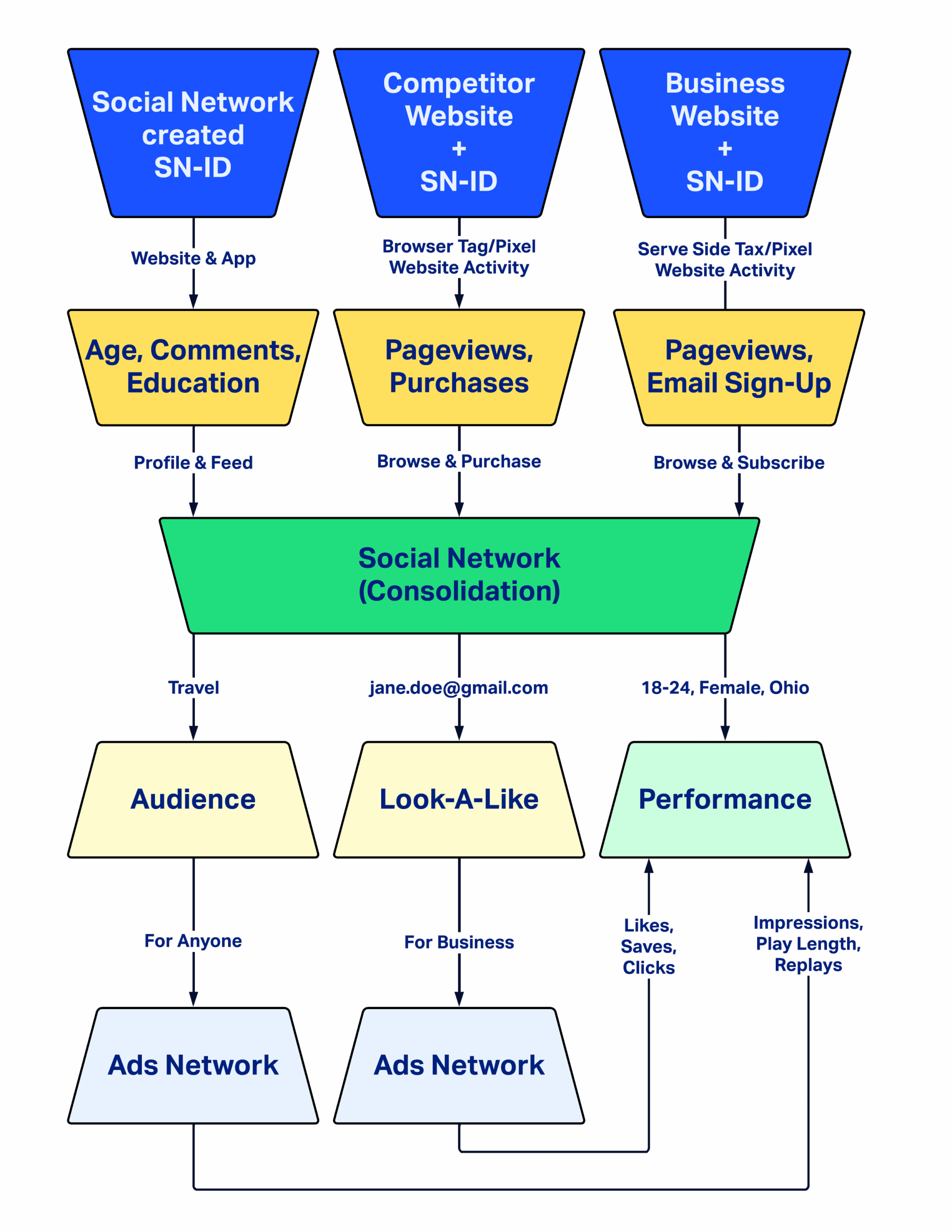
The key to many advertising campaign successes has been tied back to the amount of data that can be collected from multiple sources and collated/modeled into usable targeting groups. This means that a social media provider can combine data from multiple sources and sell it to advertisers by allowing them to target their ads to users they want to convert.
However, this has historically forced advertisers to include tracking on their websites as well, leading to more sellable data. It also can lead to inequity if used to target for bias and exclusionary reasons. Furthermore, this data is also combined with data on the social platform itself, allowing the tool in the best sense to provide personalized content that is relevant, or at the worst provide data that is misinformation or used to elicit a response.
Here is an outline of the basic process of 3rd-party cookie collection and consolidation with a Social Network Identifier (SN-ID) in a cookie:
Email Tracking Anonymization with Apple
Apple has taken steps to give their customers even more privacy by taking the data points and pings that email providers use to track interactions and anonymizing them.
Some businesses have seen the inability to optimize campaigns based on when they sell over multiple time-zones or when they have a variety of products where customers have different key interaction times. Key metrics that show high-level performance on emails, such as open rate, are also rendered obsolete.
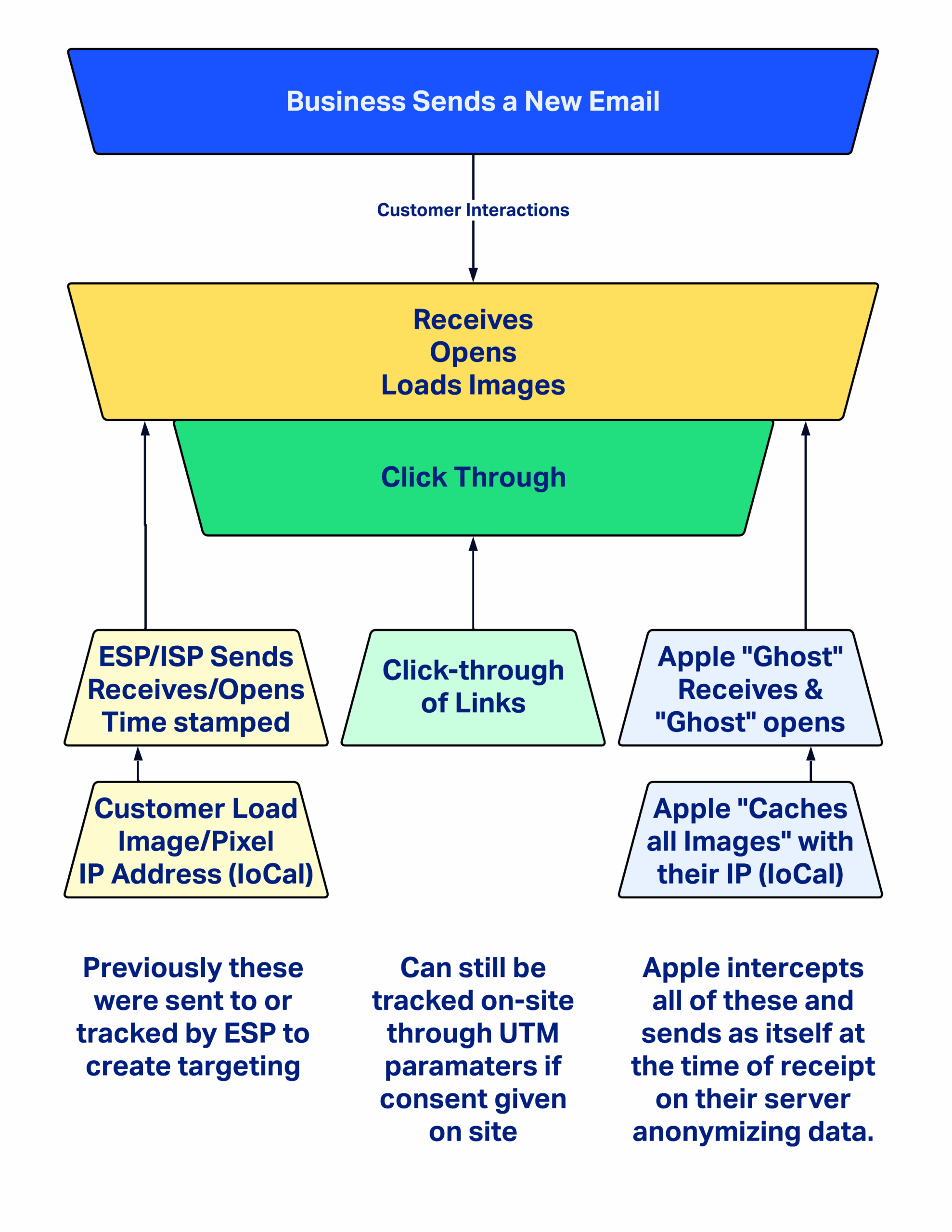
Hight-Level Goals:
- Anonymize the IP address of the customer who opens emails (Identifies one user over another)
- Pre-Cache email assets/content so customers activates are concealed (open-rate, open-time, geo-location)
- Give customer an email address that is not directly linked to them (jane.done@gmail.com is now apples523684q86q846@apple.com)
https://support.apple.com/guide/iphone/use-mail-privacy-protection-iphf084865c7/ios
Why Now?
- Because Apple devices account for 52% of email opening and they just can make that change on a whim *according to Litmus
- To make good on their promise to protect the consumer’s privacy
Other Tracking Updates with Apple
Apple has also taken further steps to expire all cookies with a new max expiration date. For first-party cookies, they will auto-expire after 24 hours. All other data is now purged after 30 days automatically. Additionally, they are adding more options in their Apps for consumers to prevent tracking unless they Opt-In on iOS devices via a prompt.
High-Level Goals:
- Protect users information from malicious storage or negligence
- Allow users to have more control over their tracking in iOS applications
- Set standard data expiration dates on stored data
Be Better On:
- Transparency
- Data Storage
- Tracking Opt-In
Anonymous 3rd Party Audience with Google
Google has taken steps to honor the anonymity / privacy of the user while providing data to businesses for marketing purposes. Examples of this would be FloC and Fledge (yes, they are named in an avian fashion!).
Some small businesses find this difficult as newer brands may not reach the capacity requirements of users or conversion to be able to receive and act on this data. Larger organizations who have optimized to be more nimble and “in the movement” may find that this data comes back at a slower pace.
high-Level Goals:
The browser, not the advertiser, holds the information about what the advertiser thinks a person is interested in.
Advertisers can serve ads based on an interest, but cannot combine that interest with other identifying information about the person—such as who they are or what page they are visiting.
Websites the person visits, and the ad networks those sites use, cannot learn about their visitors’ ad interests.
Ads can only be shown if a significantly larger group is logged to prevent micro-targeting = anonymizing your identity within a crowd.
Be Better On:
- Interest-based advertising
- Audience creation
- Conversion measurement
- Ad fraud prevention
- Anti-fingerprinting
https://blog.google/products/ads-commerce/2021-01-privacy-sandbox/
Facebook and Google Ads Verification
Major advertising networks have taken further steps to ensure that not only are they quality and qualified advertising providers, but that if there are issues that arise from advertisements there is an audit trail connected.
Some less respectable advertisers see this as a roadblock when needing an official business, contactable party and registration to be confirmed before ads can run.
High-Level Goals:
- Combat “Fake News” shared on site
- Cannot share links from ads that are not Verified Domains
- Ties in deeper political ad approvals
- Prevents misleading consumers
Be Better On:
- Transparency of messaging
- Cracking down on misleading information
- Spoofing Elimination
- Extended Audit Trails

Leave a Reply
You must be logged in to post a comment.